VMware has just released Express patches on Bash code injection Vulnerability aka “ShellShock” for most of the VMware products. However, this post is focused on express patches @vCenter Server Virtual Appliance.
Note:Please do read KBs referred below carefully corresponding to each express patch release which addresses bash vulnerability. Also note that Bash code injection vulnerability does NOT affect Windows based vCenter server.
Express patch is released on each release lines i.e. 5.0.x, 5.1.x, 5.5.x
If you are running vCenter Server Appliance 5.0.x, vCenter Server Appliance 5.0 U3b addresses Bash vulnerability:
KB:vCenter Server Appliance 5.0 U3b KB
Download from here:vCenter server appliance 5.0 U3b (Scroll down to 5.0 U3b)
If you are running vCenter Server Appliance 5.1.x, vCenter Server Appliance 5.1 U2b addresses Bash vulnerability:
KB:vCenter Server Appliance 5.1 U2b KB
Download from here:vCenter Server Appliance 5.1 u2b (Scroll down to 5.1 U2b)
If you are running vCenter Server Appliance 5.5.x, vCenter Server Appliance 5.5 U2b addresses Bash vulnerability:
KB: vCenter Server Appliance 5.5 U2a KB
Download from here:vCenter Server Appliance 5.5 U2a (Scroll down to 5.5 U2a)
VMware KB on Bash bug assessment :VMware KB on Bash Code Injection Assessment
VMware Security Advisory on Bash bug :VMware Security Advisory (Here you can also get patch details @ other VMware products)
How to quickly reproduce this bug (before applying the patch):
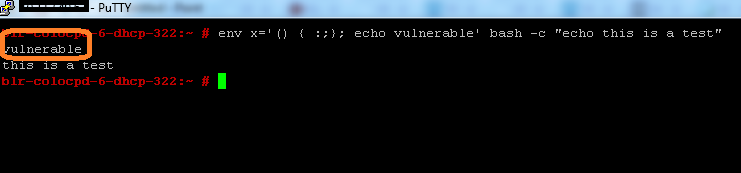
1. Login /SSH to the vCenter server virtual appliance through Putty.
2. Run this bash script :”env x='() { :;}; echo vulnerable’ bash -c “echo this is test”. It should display output as follows :
You could see both “vulnerable & “this is test” are displayed as output.
How to quickly verify this bug (after applying the patch):
1. Login /SSH to the vCenter server virtual appliance through Putty.
2. Run same bash script :”env x='() { :;}; echo vulnerable’ bash -c “echo this is test”.It should display output as follows :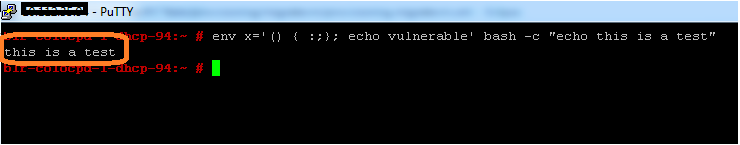
You could see only “this is test” is displayed as output. “vulnerable” should not be displayed with patch.
Learn more about Bash code injection:The Bash bug Explained

Vikas Shitole is a Senior Tech Lead at VMware by Broadcom, VCF division, India, where he leads system test efforts—including scale, stress, and resiliency testing—and drives product quality across VMware Cloud Foundation (VCF), Broadcom’s flagship private cloud platform. He is an AI and Kubernetes enthusiast, and is passionate about VMware customers and automation around vSphere and VCF. Vikas has been honoured as a vExpert for 13 consecutive years (2014–2026) for his sustained technical contributions and community leadership. He is the author of two VMware Flings, holds multiple industry certifications including VCF admin 9.0, and is one of the top contributors to the VMware API Sample Exchange, where his automation scripts have been downloaded over 50,000 times. Vikas has shared his expertise as a speaker at international conferences such as VMworld Europe and VMworld USA, and was selected as an official VMworld 2018 blogger. He also served as lead technical reviewer for the Packt-published books vSphere Design and VMware Virtual SAN Essentials. Beyond tech, Vikas is a dedicated cricketer, cycling enthusiast, and a lifelong learner in fitness and nutrition, with the personal goal of completing an Ironman 70.3